What network services does AWS provide?
AWS offers a pretty rich set of networking services that cover connectivity, traffic management, security, and hybrid/cloud-to-cloud setups.
Let’s start with the basics first.
IP Addresses
IPv4
IPv4 is the standard 32-bit address system to identify resources on a network.
Note: All public IPv4 addresses (incl. Elastic IPs) are billed at $0.005/hr.
Public IPv4
Used to access resources via the internet.
Note: EC2 instances get a new public IPv4 address on stop/start.
Private IPv4
Used within VPCs for internal communication
Note: Remains the same after instance restart.
Elastic IP
Fixed public IPv4 attached to an EC2.
Useful for stable endpoints (e.g. VPNs).
Number of available Elastic IPs
There is a soft limit on the number of available Elastic IPs per account, per region. However, if needed, more can be requested from AWS.
IPv6
IPv6 is a 128-bit addressing system where all addresses are public.
Note: IPv6 is free to use in AWS.
VPCs
A Virtual Private Network, (VPC), is an isolated AWS network where it is possible to deploy resources.
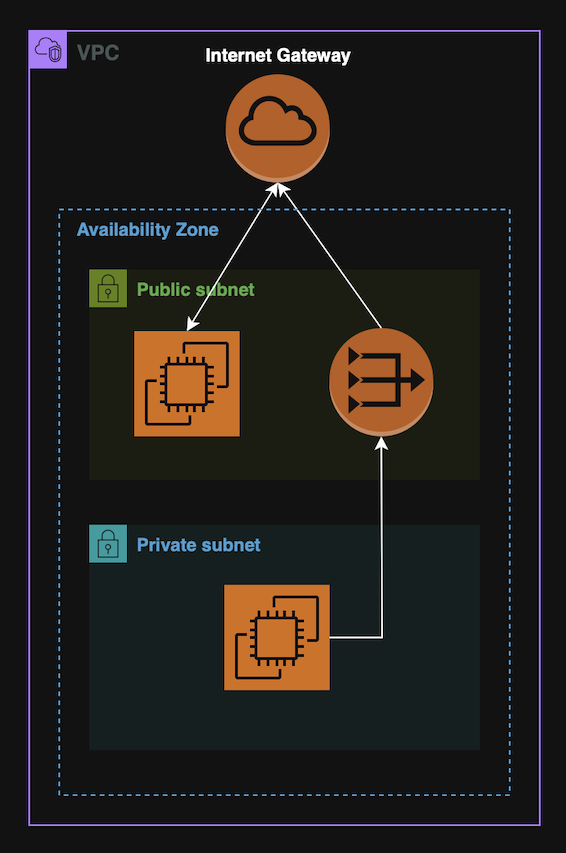
VPCs usually contain subnets. A subnet is a range if IPs inside a VPC, associated with a specific AZs.
Subnets can be:
- Public - Has route to internet Gateway;
- Private - No direct internet access. Needs NAT (Gateway or Instance).
VPC Flow Logs
VPC Flow Logs capture network traffic logs from VPC components.
Note: Can monitor traffic at different levels, (VPC, Subnet, ENI).
Use cases: Troubleshooting, auditing and monitoring.
Elastic Network Interfaces (ENIs)
An ENI is a virtual network card within a VPC that can be attached to an EC2.
ENIs can have the following configured:
- A primary private IPv4 address and one or more secondary;
- One Elastic IPv4 per Private IPv4;
- One Public IPv4;
- One MAC address;
- One or more security group.
Why do ENIs matter?
ENIs are useful because they decouple networking from the EC2 instance, allowing more flexible and resilient architectures. For instance, in case of an instance failover, the ENI can be moved to another instance, which ends up moving it’s private ip(s) as well.
Note: ENIs are AZ-scoped.
VPC Endpoints
A VPC Endpoint provides private connectivity between a VPC and AWS services without using the public internet.
VPC Endpoints improve security & latency and eliminate the need for Internet Gateways or NAT.
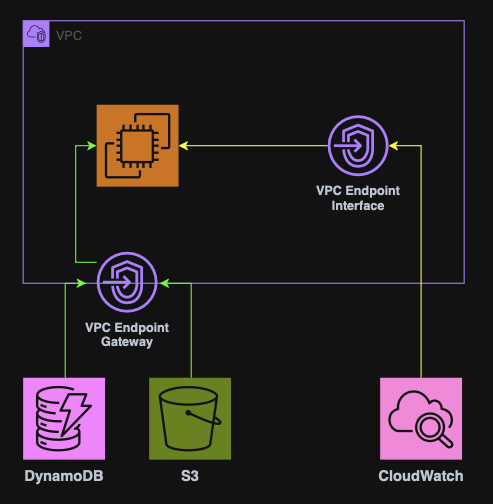
There are two types of VPC Endpoints:
Gateway Endpoint
Interface Endpoint
Used by all other services.
Connecting to VPCs
AWS allows for remote connections to be made to VPCs.
These can either be on-prem to VPC connections or VPC to VPC connections.
For on-prem to VPC connections, the following are available:
For VPC to VPC connections, the following are available:
Then there is also the Transit Gateway which connects multiple VPCs & VPNs, and AWS Client VPN for connecting user devices to a VPC.
On-prem to VPC connections
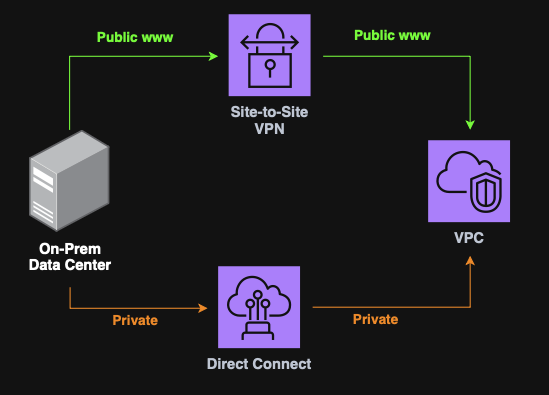
Direct Connect (DX)
Direct Connect is a private, dedicated physical connection between on-prem and AWS
Note: DX bypasses the public internet, (faster & more secure), however, it takes ~1 month to provision.
Site-to-Site VPN
Site-to-Site VPN is an encrypted connection between an on-prem Data Center and an AWS VPC over the public internet.
It required a Customer Gateway (on-prem) and a Virtual Private Gateway (AWS).
Note: May raise some latency and security considerations despite encryption.
VPC to VPC connections
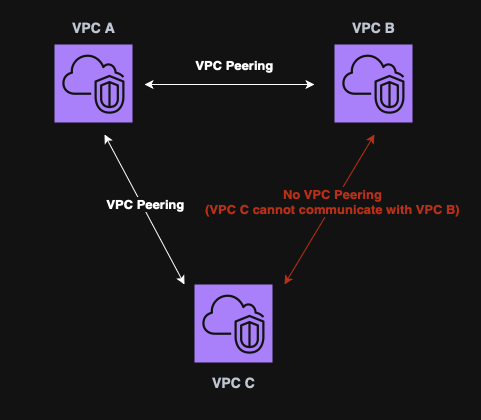
VPC Peering
VPC Peering is used to connect two VPCs privately over AWS’s network.
Key points:
- No CIDR overlapping is allowed;
- Can connecct VPCs from different regions;
- Not transitive. (VPC A ←> VPC B and VPC B ←> VPC C, does not mean that VPC A ←> VPC C).
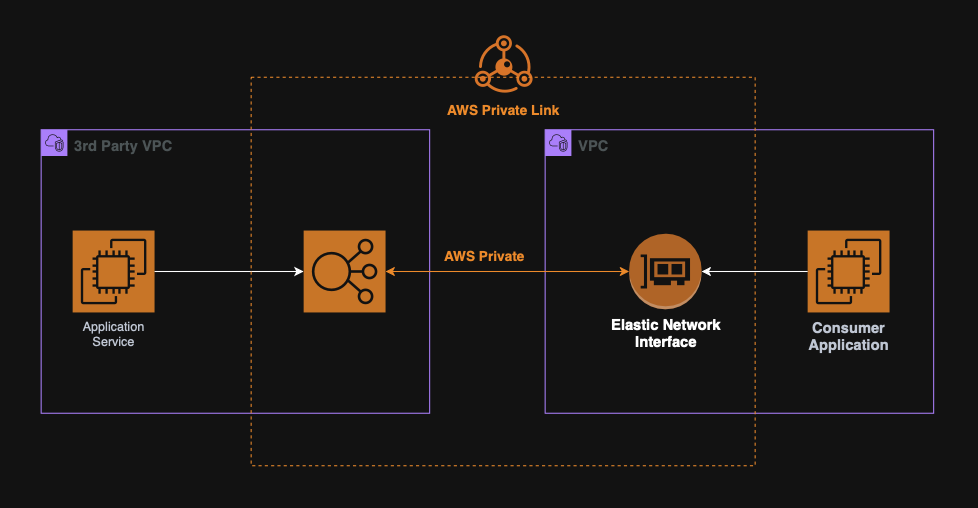
PrivateLink
PrivateLink is used to privately expose services hosted in one VPC to another VPC.
This is a more scalable and secure option that VPC Peering and great for SaaS applications or internal micro-services.
Others
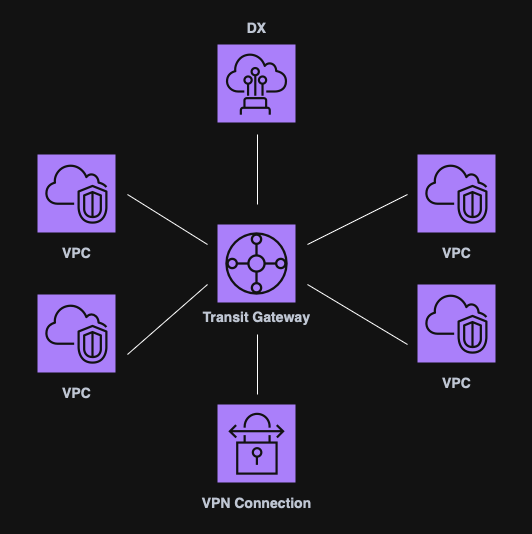
Transit Gateway (TGW)
A Transit Gateway is a centralized hub used to connect multiple VPCs and VPNs.
Key points:
- Scales better that point-to-point peering;
- Non-transitive peering replaced by a single TGW route table;
- Does not use the public internet for routing.
AWS Client VPN
The AWS Client VPN securely connects user devices, (laptops, etc.) to a VPC.
It works over the public internet and scales up to thousands of users.
VPC & Subnets firewalls
AWS provides two distinct services for setting up virtual firewalls. These are:
NACL (Network ACL)
NACL is a stateless firewall at the subnet level.
It allows for ALLOW and DENY IP based rules that are evaluated in order.
Security Groups
A Security Group is a stateful firewall, created inside a VPC, attached to a EC2 or ENI.
It is applied at the instance level and only ALLOW rules can be defined.
Security groups control:
- Access to ports;
- Authorized IP ranges. (Both IPv4 and IPv6);
- Inbound network traffic;
- Outbound network traffic.
Security group defaults
By default, a security group blocks all inbound traffic and allows all outbound traffic.
Note: A single security group can be attached to multiple instances.